Client-based access control
Client-based access control (CBAC) provides developers with a framework that enables customers to view, modify, and erase their own personally identifiable information (PII) within a repository. CBAC is used as a means of implementing the requirements under the European Union's General Data Protection Regulation (GDPR), California Consumer Privacy Act (CCPA), and other similar data privacy laws. Compliance with data protection regulations is important even when your organization is outside these places because people using your application may be located there.
With CBAC, the developer can expose PII that is tracked in a customer system of record to that specific customer. Exposing PII with CBAC allows the customer to control, modify, and erase information that they do not want to store in an application's database.
Examples of information in a customer system of record that can be exposed to the client it belongs to includes: the customer name, addresses, social security number (SSN), or credit card numbers.
The developer decides what information the customer can modify and erase. For example, based on your business requirements and compliance with various regulations and laws concerning selling alcohol and renting vehicles, the developer may not allow users to modify or erase their date of birth.
The General Data Protection Regulation (EU)
In the following image, click the + icons to learn about the seven principles outlined in GDPR that an organization must follow to achieve compliance.
Client-based access control application structure
CBAC in Pega Platform involves a Pega GDPR request management application (RMA) and one or more Pega Platform applications. The RMA is where client rights are displayed, and the CBAC requests originate. The client interacts with the RMA, and the RMA interacts with the specified repository or repositories to manage the data itself. Client requests to rectify, erase, or limit personal data usage are made by using REST APIs. The Pega Platform applications are where personal data is used and stored in a Pega database and where client requests are enforced.
In the following image, click the + icons to learn more about the case processing by a GDPR request management application that supports multiple Pega applications.
The implementation of a GDPR request management application and multiple Pega Platform applications enables CBAC. CBAC allows customers to manage their personal data and delete information that the business does not deem essential.
Client-based access control rules
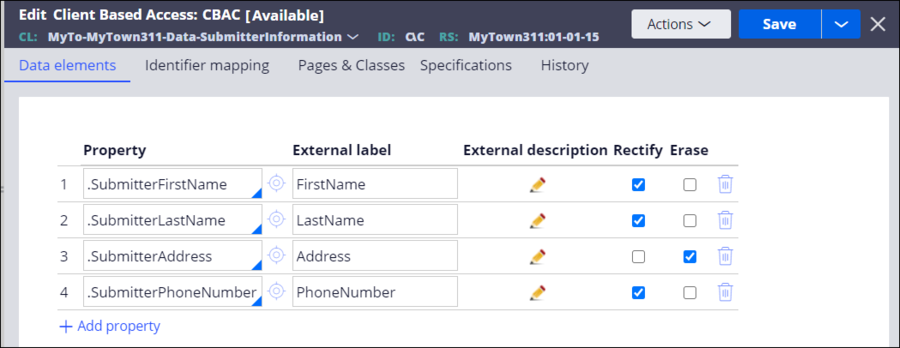
To use CBAC, developers create a client-based access rule for each class where personal data is stored. For example, if personal data and identifiers are in the same class, the developer creates one CBAC rule for the entire application. If personal data and identifiers are stored in multiple classes, the developer creates a CBAC rule for each class.
CBAC rules describe the personal data and identify where the data is stored in the Pega database. Adding a property to the CBAC policy rule enables view access for the property. Developers can add privileges to allow application users to perform the Rectify and Erase actions on the data by enabling the corresponding checkboxes.
Developers can allow application users to identify how they consent to their personal data being used. For example, customers of a bank's online application can allow the bank to use their personal data for functions within the online banking application, but not for marketing purposes.
Check your knowledge with the following interaction.
Want to help us improve this content?